Most people skip the fine print. However, if you want real online privacy, you must learn how to read a VPN privacy policy carefully. Marketing pages promise “no logs” and “total anonymity,” yet the legal document often tells a different story.
A privacy policy explains what data a provider collects, how it stores that data, and when it may share information. Therefore, understanding this document helps you avoid misleading claims.
In this guide, you will learn how to read a VPN privacy policy step by step, identify red flags, and confidently choose a provider that protects your digital footprint long term.
Why Privacy Policies Matter More Than Marketing
Homepage slogans focus on benefits. Privacy policies focus on legal reality.
While promotional material highlights encryption and speed, the policy reveals data handling practices. Consequently, this document determines whether your activity remains private.
If a VPN stores connection logs, IP addresses, or timestamps, your anonymity weakens. Even minimal metadata can identify patterns over time.
Therefore, learning to read a VPN privacy policy gives you the power to verify claims instead of relying on branding alone.
Start With the Data Collection Section
The most important section usually appears under “Information We Collect.”
Look for Activity Logs
A trustworthy provider states clearly that it does not collect browsing history. If you see vague phrases like “may collect usage data,” examine the wording carefully.
Check for IP Address Storage
Temporary or persistent IP storage creates privacy risks. Therefore, confirm whether the company logs incoming or outgoing IP addresses.
When you read a VPN privacy policy thoroughly, you often uncover small but critical distinctions.
Understand Connection Logs vs. Usage Logs
Some providers claim “no logs” while still collecting connection metadata.
Connection logs may include timestamps, bandwidth usage, or server locations. Although these seem harmless, they can identify users when combined with other data.
Usage logs, on the other hand, track websites visited or files downloaded. These create greater risk.
Distinguishing between these categories helps you read a VPN privacy policy accurately rather than relying on broad claims.
Look for Data Retention Periods
Retention policies reveal how long information remains stored.
If a provider stores data “for troubleshooting purposes,” check the duration. Hours may differ significantly from months.
Short-term aggregated analytics often present lower risk. However, persistent storage contradicts strong privacy promises.
Whenever you read a VPN privacy policy, pay close attention to specific timeframes rather than general language.
Examine Third-Party Sharing Clauses
Many VPNs use external services for payments, analytics, or marketing.
Payment Processors
Reputable providers often rely on third-party payment systems. However, ensure financial data remains separate from browsing activity.
Analytics Tools
Some VPN apps include crash reporting tools. While these help improve performance, they may collect device identifiers.
When you read a VPN privacy policy, confirm that third-party data cannot link to your browsing sessions.
Check for Independent Audits
Privacy policies sometimes mention external audits.
Independent firms verify whether no-logs claims align with technical infrastructure. Therefore, references to audits strengthen credibility.
However, confirm whether audit reports are public. Transparent documentation improves trust.
As you read a VPN privacy policy, look for specific audit names and dates rather than vague references.
Jurisdiction and Legal Compliance
The country where a VPN operates affects its obligations.
Some nations enforce mandatory data retention. Others protect digital privacy more strongly.
However, jurisdiction alone does not guarantee anonymity. Infrastructure design still matters.
When you read a VPN privacy policy, identify the company’s headquarters and legal registration details.
Investigate Data Requests and Transparency Reports
Many providers publish transparency reports outlining government requests.
If reports consistently state “no data available,” that supports no-logs claims.
Additionally, warrant canaries may indicate whether secret orders occurred.
Reviewing these elements while you read a VPN privacy policy helps confirm long-term reliability.
Understand Technical Terminology
Privacy policies often use technical language.
Terms like “aggregated data,” “anonymized information,” and “pseudonymous identifiers” may appear harmless. However, their definitions vary.
Aggregated data combines multiple users’ information. True anonymization removes identifiable markers permanently.
If definitions remain unclear, research further. The more precisely you read a VPN privacy policy, the fewer surprises you encounter later.
Watch for Ambiguous Language
Certain phrases signal caution.
Statements like “we may collect certain information to improve services” lack specificity. Therefore, seek detailed explanations.
Similarly, policies that allow broad interpretation create uncertainty.
Clear and direct wording indicates stronger commitment. Therefore, carefully read a VPN privacy policy for clarity rather than marketing tone.
Review Account and Registration Requirements
Some VPNs require minimal personal information. Others demand full names and addresses.
Providers focused on privacy often accept cryptocurrency or anonymous payments.
When you read a VPN privacy policy, evaluate whether account creation links your identity to usage data.
Limiting required information reduces long-term exposure.
Check Data Security Measures
A good policy explains how data remains protected.
Look for references to encryption standards such as AES-256. Additionally, confirm whether servers operate on RAM-only infrastructure.
Security measures prevent stored data from becoming accessible to attackers.
Therefore, read a VPN privacy policy for technical details rather than general statements.
Confirm Log Deletion Procedures
Some providers temporarily log data for troubleshooting.
If so, check how they delete it. Automatic deletion policies reduce risk significantly.
Manual deletion processes may introduce human error.
When you read a VPN privacy policy, ensure deletion timelines appear clearly defined.
Identify Red Flags
Avoid providers that:
Use overly broad collection clauses
Fail to define retention periods
Lack transparency reports
Avoid mentioning audits
Recognizing these signs protects you from weak privacy commitments.
Therefore, always read a VPN privacy policy carefully before subscribing.
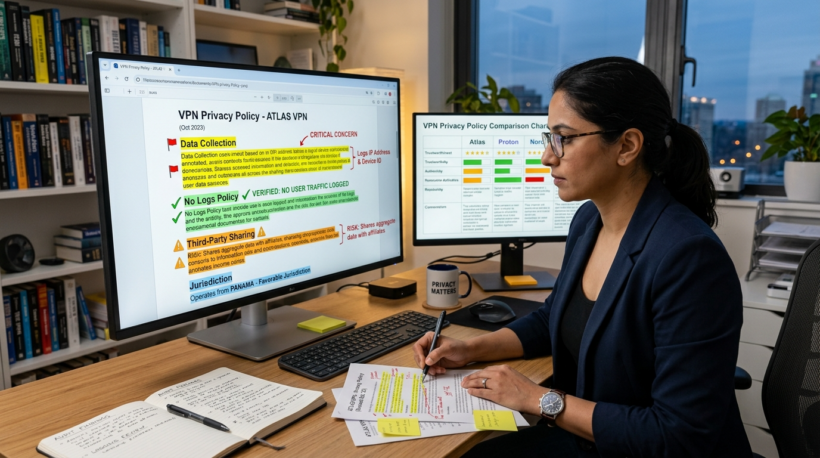
How to Compare Multiple Policies
Comparing policies side by side clarifies differences.
Highlight sections covering data collection, retention, and sharing.
Additionally, check update dates. Recently revised policies may reflect improved transparency.
Taking time to read a VPN privacy policy across providers helps you make informed decisions.
Create a Simple Evaluation Checklist
To simplify analysis, ask:
Does the provider store IP addresses?
Are connection logs retained?
How long is data stored?
Are audits available?
Is jurisdiction privacy-friendly?
Answering these questions ensures you read a VPN privacy policy methodically rather than casually.
Why Ongoing Monitoring Matters
Privacy policies can change.
Providers update terms periodically. Therefore, review policies annually to confirm continued compliance.
Subscribe to transparency updates when possible.
Staying informed ensures you continue to read a VPN privacy policy proactively rather than reactively.
Final Thoughts on Evaluating VPN Policies
Online privacy depends on informed decisions. Marketing promises rarely tell the full story.
When you read a VPN privacy policy thoroughly, you uncover details about logging, retention, and data sharing.
Small clauses often determine whether your activity remains private long term.
Therefore, approach each policy carefully and critically. By mastering how to read a VPN privacy policy, you protect your digital identity with confidence.
FAQ
- Why is the privacy policy more important than marketing claims?
Marketing highlights benefits, but the policy legally defines data collection and retention practices. - What is the difference between connection logs and usage logs?
Connection logs track metadata like timestamps, while usage logs record browsing activity. - Are independent audits necessary?
Audits provide third-party verification that no-logs claims match technical reality. - Does jurisdiction affect my privacy?
Yes, local laws influence whether companies must retain user data. - How often should I review a provider’s data practices?
Check annually or whenever the company updates its policy to ensure continued compliance.